Milestone Year
1977
RSA: Constructing Public Key Encryption and Digital Signatures Schemes
Classical encryption schemes, used since the times of Caesar, rely on a secret key that is shared by the communicating parties but is unknown to the adversary, who wishes to learn the contents that is hidden in the encrypted communication. This model raises the problem of agreeing on the secret key or communicating it from one party (who generates it) to the other.
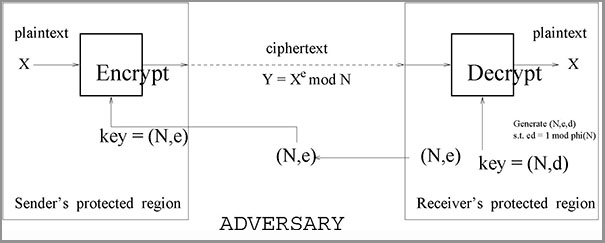
In contrast, the RSA is an encryption scheme that relies on two keys: One key is used for encryption, which may be publicized and hence is known to the adversary, whereas a second key is used for decryption. Indeed, it must be infeasible to derive the decryption key from the encryption key, while corresponding pairs of keys are easy to generate (by the designated receive, who may publicize the encryption key and keep the decryption key secret). In the RSA scheme, the infeasibility of deriving the decryption key is based on the conjectured intractability of factoring large integers.
The same work also proposed a method for producing digital signatures such that the signatures can be verified based on a public verification key but cannot be efficiently produced without a corresponding signing key.
Public-key encryption and digital signatures were envisioned a year before the RSA, but the RSA was the first proposed implementation that withstood the test of time. Indeed, the RSA is used in practice till this very day, and has been a source of inspiration to much of the subsequent research in cryptography.
In 2002 the RSA served as the the basis for the bestowing of the Turing award on its inventors.
RSA